Get your personal identity verification card (also known as a credential, common access card, LincPass, smart card, badge, etc. depending on your agency).
For applicants
Enhance security, reduce identity fraud, and protect the privacy of government employees and contractors by onboarding with the USAccess program.
For agency customers
About your PIV card
Your PIV card is compliant with the Homeland Security Presidential Directive 12 and the Federal Information Processing Standards and provides a secure and reliable form of government identification. Federal employees and contractors use PIV cards to access facilities and systems. PIV cards may also be known as a credential, common access card, LincPass, smart card, badge, or something else depending on your agency.
Proper card storage
Do not store your card in your wallet, purse, or any unapproved plastic card holder or sleeve, as this may damage the card. You must store it in the electromagnetically opaque sleeve or holder provided at pickup. Contact your sponsor if you did not get an approved PIV card holder.
Your card’s features
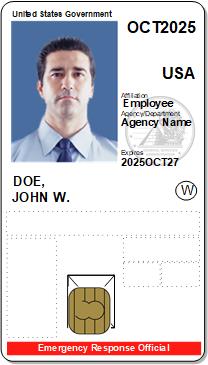
All PIV cards have common visual elements that are printed in the same location regardless of the agency.
Information that’s visible on your card includes:
- Your agency seal.
- Your agency’s return address.
- A picture of your face.
- Your physical characteristics (height, eye color, and hair color).
- The expiration date of the physical card.
- Your full name.
- Your agency.
- A serial number.
Chip contents
The integrated circuit chip on your card stores:
- x509 PKI digital certificates such as PIV authentication, card authentication, digital signature for documents, and encryption for emails.
- Two interoperable fingerprint templates.
- A digital image of your face.
If a recipient’s email provider can accept PKI for digitally signed emails or documents, the recipient can verify a sender’s digital signature and view and open documents.
The physical card expires after five years but the certificates expire three years from the date of activation. Contact your sponsor if you need your card reissued before then.
Tell us what you think

 U.S. General Services Administration
U.S. General Services Administration